Embry-Riddle Cybersecurity Student Earns Place on Boeing’s Security Hall of Fame

Imagine you’re a pilot.
In preparation for an upcoming flight, you open your portable Electronic Flight Bag (EFB) to review your flight plan. Suddenly, air traffic starts displaying on your map and continues flooding in until the app crashes. You attempt to re-open the app, but it won’t load. Is your EFB broken? Should you cancel your flight? More likely, your EFB got hit with a denial-of-service attack while connected to an insecure guest network.
Embry-Riddle Aeronautical University student Kestrel Carlough wanted to prevent air-traffic-related threats like these when he began a recent research project, under the direction of Dr. Krishna Sampigethaya, department chair and associate professor of Cyber Intelligence and Security at Embry-Riddle’s Prescott Campus.
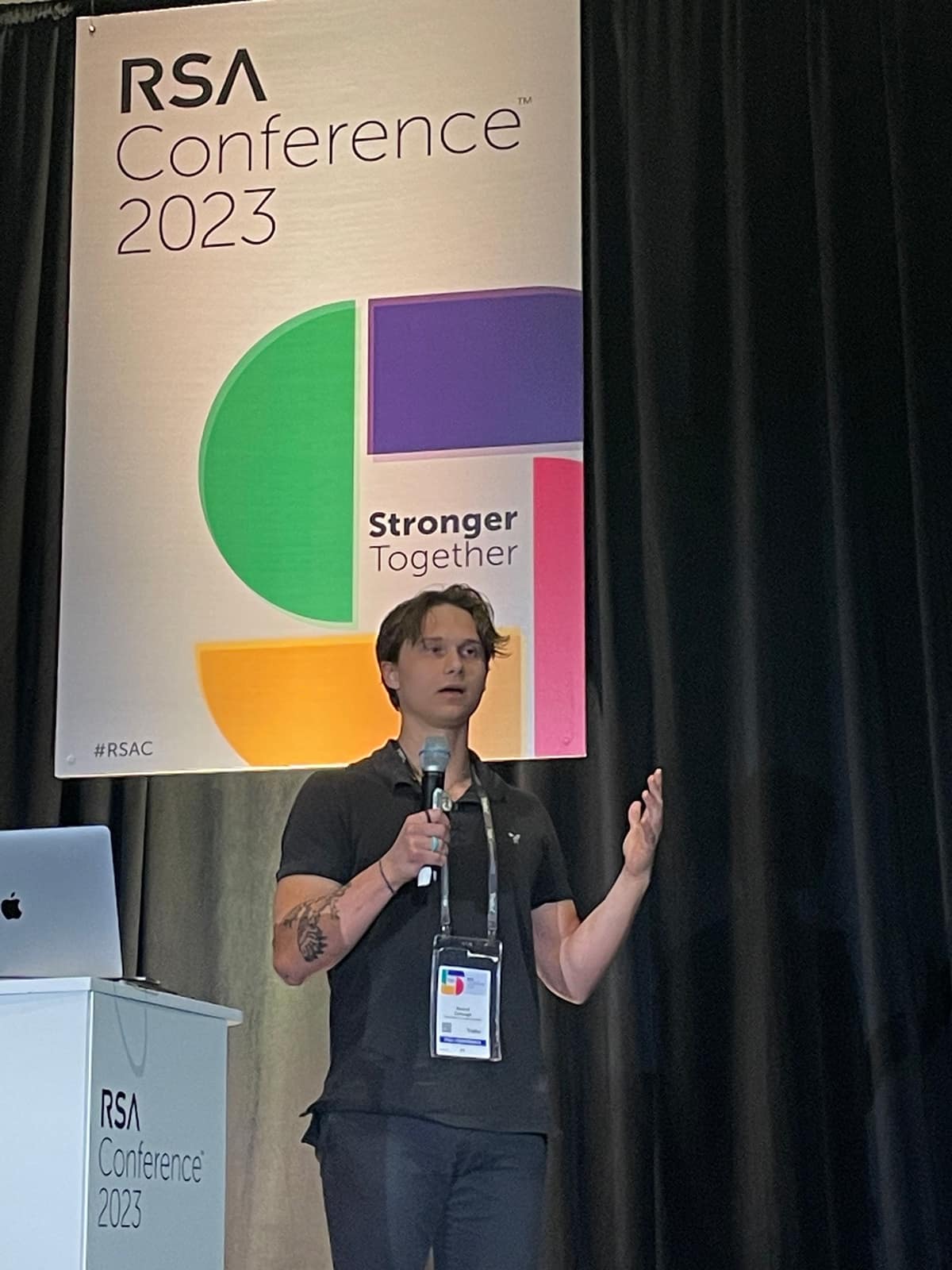
Embry-Riddle student Kestrel Carlough was the only undergraduate in the nation invited to present research to a panel of industry leaders at the recent RSA conference, which attracts over 40,000 attendees. (Photo: Kestrel Carlough)
Specifically, Carlough concentrated on wireless network interfaces, which led him to discover a security vulnerability in a popular EFB app. He then reported the issue to The Boeing Company, and thanks to his efforts, the vulnerability has been resolved.
“Kestrel was recognized by Boeing for helping them fix a vulnerability in one of their leading apps,” said Dr. Sampigethaya. “They were so impressed with him and his work that they acknowledged him and our university in their Security Hall of Fame.“
“Airlines are using EFBs to go paperless in their operations, and pilots use EFBs to be aware of weather data, air traffic and other flight-planning information,” Carlough explained. “Most students and general aviation pilots also use EFB [mobile] apps.”
Carlough initially focused on avenues to penetrate the app, which involved controlling the display of air traffic information. He discovered a way to imitate or “spoof” legitimate flight data, creating the ability to draw his own fictitious airplanes as tiny blue dots.
“I was sitting in the library one day with a friend who was doing some flight planning on his EFB,” said Carlough. “And just to mess with him a bit, I wanted to draw a smiley face across his flight map with these tiny blue dots. So, I crafted the information and sent it over, and his application actually crashed.”
What started as a simple prank revealed gaps in the system that, Carlough realized, could have real-world implications. There were no limits on the number of aircraft the application could draw, it turned out.
“This isn’t good,” Carlough said. “Pilots need to know things like where they are and if other planes are coming toward them in real time.”
Carlough was quick to point out that this type of attack could only happen if an attacker was on the same local wireless connection as the EFB.
“In reality, this is unlikely to happen when an airplane is in the air,” he said, adding that the likelier location of such an attack would be near an airport terminal.
“Kestrel was really good at understanding the EFB app protocols and how information is being communicated between different devices in the aircraft wireless network,” fellow Cybersecurity student Tyler Schreffler said. “I give him a lot of credit for finding that issue because it exposed a genuine vulnerability in a commercial EFB application.”
To understand the impact of the potential security problem, Carlough looked to international airworthiness security standards, which certify the integrity and availability of data that are transferred between systems required for flight and provide guidance on how to assess and mitigate malicious attacks of aircraft systems.
“Leveraging the guidance of the standards, the determination was made that the vulnerability could lead to a minor impact,” Carlough said. “To be clear, there are highly redundant systems on aircraft. EFBs are really used for paperless operations, aircraft system weight savings and ease of pilot workload, rather than being an actual safety-critical system.”
He submitted a vulnerability disclosure to Boeing and worked with its security team to explain the issue. He was notified by Boeing in February 2023 that the vulnerability was fixed.
“I have validated myself that this type of attack is no longer possible,” Carlough said.
As a result of his discovery, Carlough was selected as an RSA Security Scholar, which spotlights him among the brightest up-and-coming cybersecurity professionals in the nation. He was also invited to attend the recent RSA conference, a global cybersecurity event that attracts more than 40,000 attendees annually, where he was the only undergraduate student in the country, and one of only four students total, invited to present his work to a panel of industry judges in a poster session. (His presentation can be viewed online.)
“I came to Embry-Riddle and got my bachelor’s degree in Cyber Intelligence and Security. I have now decided to stay here for my master’s degree mostly because of the faculty,” Carlough said. “They’re great. They will work with you and provide you with incredible opportunities.”
Carlough is a National Science Foundation (NSF) CyberCorps Scholarship for Service (SFS) scholar and Schreffler is a Department of Defense (DoD) Cyber Scholarship Program (CySP) scholar.

 Everly Chadwick
Everly Chadwick